Avec les frimas de l’hiver s’installe l’éternelle quête de la doudoune idéale. Entre confort thermique …

S'informer c'est s'instruire
S'informer c'est s'instruire

Avec les frimas de l’hiver s’installe l’éternelle quête de la doudoune idéale. Entre confort thermique …
Dans l’écosystème digital actuel, l’optimisation SEO est la pierre angulaire de la visibilité en ligne. …

La mauvaise haleine, ou halitose, est un problème qui peut affecter n’importe qui. Elle peut …

Le Mexique est une mosaïque de cultures, une symphonie de saveurs et une palette de …

À Wambrechies, le portage salarial s’impose comme une solution moderne pour allier flexibilité professionnelle et …

Lorsque la vie vous impose un changement, comme un déménagement, des travaux de rénovation, ou …

Imaginez embrasser l’horizon marin sur tous les continents, accoster sur des rivages exotiques et réveiller …

L’or est une énigme du temps, séduisant et mystérieux, son éclat n’a cessé de captiver …

Ah, Montalivet… Son air marin, ses plages étendues, sa douceur de vivre. Et parmi les …

Face à la dictée du brevet, l’angoisse des élèves est palpable, pourtant, une préparation adéquate …

Lorsqu’une urgence médicale survient en pleine nuit, la connaissance des bons protocoles peut faire toute …

Face à une urgence médicale nocturne ou un week-end, la recherche d’une pharmacie ouverte devient …

L’éclatante cité de Montpellier, avec son patrimoine culturel, son dynamisme économique et son cadre de …

Dans une ère où les marchés financiers sont aussi volatils que l’humeur du ciel, investir …
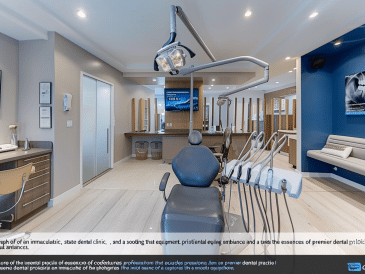
À la recherche d’une expertise dentaire inégalée à Vaudreuil? La Clinique dentaire Charles Trottier synthétise …

Le Pays Basque, cette terre de contrastes nichée entre océan et montagnes, a longtemps été …

Vous vivez à Paris et la radio est votre compagne au quotidien? Ce guide exhaustif …

Chercher l’âme sœur en ligne peut être intimidant, surtout lorsque vous recherchez une relation sérieuse …

Lorsque la chaleur estivale s’invite dans nos jardins, la piscine devient rapidement le centre de …

L’émeraude, cette pierre précieuse d’un vert profond évoquant la beauté naturelle de la Terre, a …

La recherche de bien-être et la quête d’une meilleure santé physique passent souvent par le …

Dans un monde où la concurrence est sans cesse croissante, les entreprises sont continuellement à …

Dans notre quête incessante de bien-être et d’harmonie, le massage s’impose comme une pratique ancestrale, …

La Camargue, terre de traditions et de nature sauvage, attire chaque année des milliers de …

Envie de vous évader dans les montagnes et de respirer l’air pur des Alpes françaises …

Plonger dans l’univers des maillots de bain n’est pas qu’une simple affaire de mode, c’est …

Bienvenue dans l’univers des vélos tous terrains (VTT), où chaque sentier devient une invitation à …

L’intégration des normes environnementales dans le secteur de la construction n’est plus une option mais …

À l’heure où le smartphone devient le principal moyen d’accès à internet, optimiser son site …

Lyon se distingue également par son marché immobilier de luxe dynamique et attrayant. Que vous …
Toulouse, la captivante ville rose, continue de charmer tant les résidents que les investisseurs grâce …

Madrid, ville aux mille couleurs, vibre au rythme de ses places animées, ses avenues historiques …

L’immobilier a longtemps été perçu comme une valeur refuge pour les investisseurs. Et pour cause, …

Au cœur d’un marché de l’emploi en santé en constante évolution, les professionnels du secteur …

Organiser leur mariage est une tâche qui allie passion et précision. C’est un moment où …

Bienvenue dans le monde scintillant des yachts de luxe, où le bleu profond de l’océan …

Chers aventuriers des temps modernes, bienvenue dans un havre où l’océan atlantique caresse les côtes …

Les punaises de lit sont de petits insectes nuisibles qui se nourrissent du sang des …

Dans le vaste univers des programmes de fidélité, où la concurrence est féroce et les …

À l’aube de 2023, la mode éthique ne cesse de gagner du terrain dans l’univers …

La santé bucco-dentaire est une composante essentielle de notre bien-être général. Si le rôle du …

Se réveiller face aux montagnes ardéchoises, écouter le murmure de la rivière tout en prenant …

Bienvenue dans l’écrin de saveurs et de patrimoine qu’est Sarlat-la-Canéda, où le temps s’égrène au …

Dans une époque où l’innovation est au cœur de l’aménagement de nos espaces de vie, …

Le Pays basque, avec ses panoramas pittoresques et sa culture vibrante, est également un terreau …

Ah, Gourette ! Située au cœur des majestueuses Pyrénées, cette station est une destination prisée …

À l’aube de 2024, l’univers des dashcams continue d’évoluer à un rythme effréné, poussé par …

À mesure que les feuilles tombent et que les premiers flocons de neige annoncent l’arrivée …

Lorsque l’on évoque l’investissement dans l’immobilier, une multitude de stratégies s’offrent à vous. Parmi elles, …

Dans le labyrinthe incessant des avancées technologiques et des pratiques commerciales novatrices, les entreprises recherchent …